Azure Database for MySQL is a fully managed relational database service built on the MySQL community edition. It handles provisioning, patching, backups, and scaling automatically, and is available in two deployment modes: Flexible Server and Single Server. Connecting Azure Database for MySQL to Databox lets you pull data directly from your managed database, build datasets using SQL queries, and visualize business-critical figures alongside data from your other connected tools.
If you've already established a connection, you can reuse it to add new data sources to your Databox account.
Databox only reads data from your database — it never writes to it. Create a dedicated MySQL user with SELECT-only privileges scoped to the Databox IP address. You can run these commands using the Query editor in the Azure portal, or via a MySQL client connected to your instance.
MySQL 8.0+ (modern syntax):
CREATE USER 'databox'@'52.4.198.118' IDENTIFIED BY 'your_secure_password';
GRANT SELECT ON your_database.* TO 'databox'@'52.4.198.118';
FLUSH PRIVILEGES;MySQL 5.7 (legacy single-statement syntax):
GRANT SELECT ON your_database.* TO 'databox'@'52.4.198.118' IDENTIFIED BY 'your_secure_password';
FLUSH PRIVILEGES;Replace your_database with the name of the database you want to connect, and your_secure_password with a strong password. If you need to grant access to multiple databases, repeat the GRANT statement for each one.
Databox connects to Azure Database for MySQL over a public endpoint. The steps differ depending on whether you are using Flexible Server or Single Server.
Flexible Server:
- In the Azure portal, go to your Azure Database for MySQL Flexible Server resource.
- Under Settings, click Networking.
- Under Connectivity method, select Public access (allowed IP addresses).
- Click Save to apply the change.
Single Server:
- In the Azure portal, go to your Azure Database for MySQL Single Server resource.
- Under Settings, click Connection security.
- Set Allow access to Azure services to No (unless required for other integrations).
- Confirm that Public access is enabled. If not, enable it and click Save.
Azure Database for MySQL uses firewall rules to control inbound network access. Add a rule that permits connections from the Databox IP address.
Flexible Server:
- In the Azure portal, go to your Flexible Server resource.
- Under Settings, click Networking.
- Under Firewall rules, click Add current client IP address or click Add firewall rule to enter a custom range.
- Set the Start IP address and End IP address both to
52.4.198.118. - Give the rule a name (e.g.,
Databox) and click Save.
Single Server:
- In the Azure portal, go to your Single Server resource.
- Under Settings, click Connection security.
- Under Firewall rules, click Add client IP or enter values manually:
- Rule name:
Databox - Start IP:
52.4.198.118 - End IP:
52.4.198.118
- Rule name:
- Click Save.
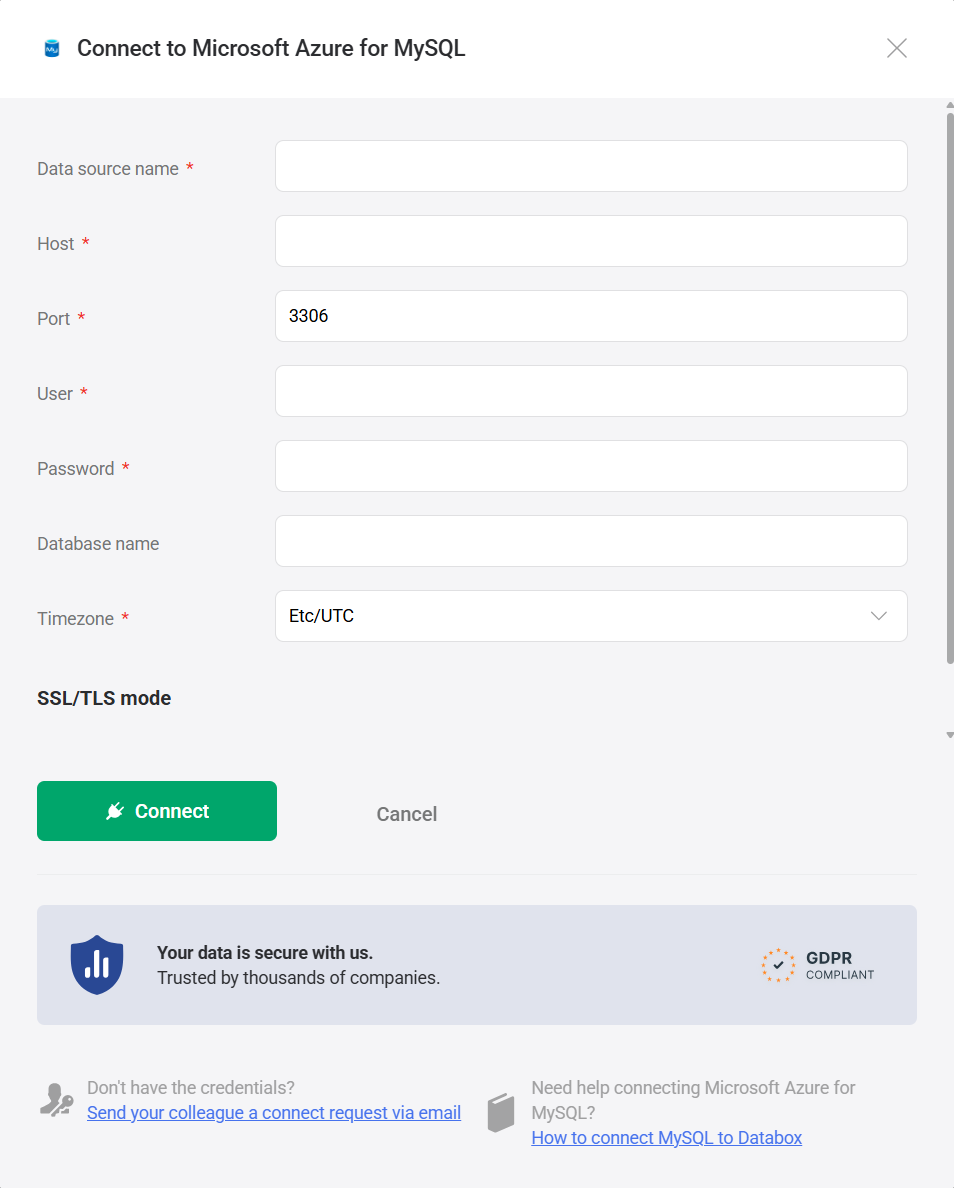
- In Databox, go to Data Sources > + New connection.
- Search for Microsoft Azure for MySQL and click Connect.
- Fill in the connection form:
- Data source name — a label for this connection in Databox.
- Host — the fully qualified server name of your Azure MySQL instance, found on the Overview page in the Azure portal (e.g.,
myserver.mysql.database.azure.com). - Port — the port your instance listens on. The default for Azure Database for MySQL is
3306. - User — the MySQL username created in Step 1. For Flexible Server, use the plain username (e.g.,
databox). For Single Server, Azure may require the formatusername@servername(e.g.,databox@myserver). - Password — the password for that user.
- Database name (optional) — the specific database to connect to. Leave blank to connect at the server level.
- Timezone — the time zone used to interpret date values in query results. Defaults to
Etc/UTC.
- Select an SSL/TLS mode (see SSL/TLS below).
- Click Connect.
Databox offers three SSL/TLS modes when connecting to a database. Choose the one that matches your server's configuration.
| Mode | Description |
|---|---|
| None | The connection is made without SSL/TLS encryption. Use this only when your server does not have SSL enabled. |
| Use SSL/TLS with provider CA bundle | The connection uses SSL/TLS and authenticates the server using a regional CA bundle managed by your cloud provider (for example, Amazon RDS). When you check Verify server certificate using regional CA bundle, an additional CA certificate bundle (ssl-ca) field appears, where you can paste your provider's CA certificate. |
| Use SSL/TLS with custom certificates | The connection uses SSL/TLS with certificates you supply directly. When Verify server certificate is checked, you must provide a CA certificate (ssl-ca). You may also supply a Client certificate (ssl-cert) and Client private key (ssl-key) for mutual TLS. If Verify server certificate is unchecked, only the client certificate and private key fields are shown. |
Azure Database for MySQL enforces SSL/TLS connections by default. To use SSL with server certificate verification, download the DigiCert Global Root CA certificate from the Azure SSL connectivity documentation and paste its contents into the CA certificate bundle (ssl-ca) field in Databox. For step-by-step instructions on configuring each SSL mode, see Enable SSL/TLS for your database connection.
The MIcrosoft Azure for MySQL integration supports the creation of datasets, which allow you to define and shape the specific data you want to use for reporting in Databox. Datasets make it easier to focus on the most relevant information, enabling you to filter, visualize, and analyze metrics across projects, teams, and clients without writing complex queries each time.
- Select a table: Pick the appropriate schema within that database.
- Select columns: Browse and select the specific columns (fields) from your tables or views to include in your dataset. These columns define the structure and content of your dataset.
For more advanced use cases, you can write a custom SQL query instead of selecting columns manually. This allows you to:
- Join multiple tables
- Apply filters and aggregations
- Format or transform data before importing it into Databox
Your query must return a valid tabular result to be used as a dataset.
- Azure Database for MySQL documentation — Official Microsoft docs for Azure Database for MySQL, covering Flexible Server and Single Server deployment modes, connectivity, security, backups, high availability, and monitoring.
- Azure Database for MySQL Flexible Server networking overview — Guidance on public access, private access (VNet integration), and firewall rule configuration for Flexible Server.
For comprehensive details on metrics, data availability, templates, specifications, usage guidelines, and other key information, refer to the resources listed below.
FAQ
Does Databox support Azure Active Directory (Entra ID) authentication?
No. Databox connects to Azure Database for MySQL using standard MySQL username and password authentication. Azure Active Directory (Microsoft Entra ID) authentication is not supported. Make sure the user you create in Step 1 uses standard MySQL authentication, not Azure AD authentication.
What username format should I use for Azure Database for MySQL?
The required format depends on your deployment mode. Flexible Server accepts plain usernames (e.g., databox). Single Server requires the format username@servername (e.g., databox@myserver), where myserver is the part of your hostname before .mysql.database.azure.com. If the connection fails with an authentication error, check that you are using the correct format for your deployment mode.
What should I do if Databox cannot connect to my Azure MySQL instance?
Check the following in order:
- Public access is enabled on the instance (under Networking for Flexible Server, or Connection security for Single Server).
- A firewall rule exists with both start and end IP set to
52.4.198.118. - The MySQL user was created with
'databox'@'52.4.198.118'as the host — not'%'or'localhost'. RunFLUSH PRIVILEGES;after any user or grant changes. - If SSL enforcement is enabled on the instance, select an SSL mode other than Disabled in the Databox connection form.